Collagen supplements have gained popularity in the health and wellness industry in recent years. But before adding them to your …



Collagen supplements have gained popularity in the health and wellness industry in recent years. But before adding them to your …

Have you ever had trouble verifying your identity on 188Bet? It can be a frustrating and time-consuming process, but it …
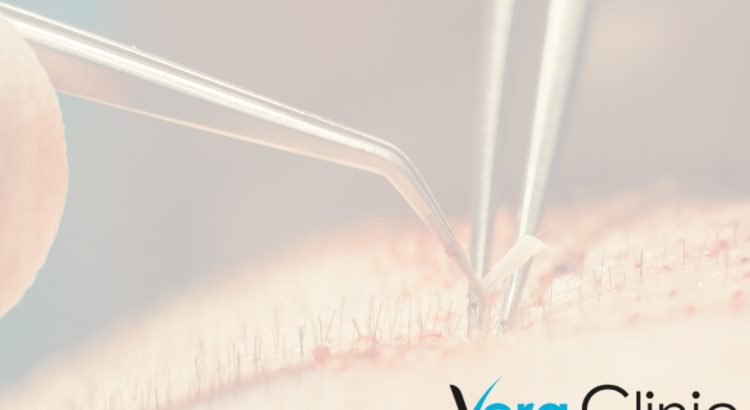
In recent years, hair transplants have become a popular remedy for baldness. However, many variables affect the outcome of these …

동료 베터들과 위험을 감수하는 사람들을 환영합니다! 운명이 만들어지고 꿈이 이루어지는 짜릿한 온라인 베팅의 세계에서 우리가 결코 간과해서는 안 될 중요한 …

“밤알바에서의 커리어 빌딩: 성공적인 전략과 팁” 여러분, 밤에 일하는 알바생들을 위한 비법이 도착했습니다! 어두운 밤에 활기차게 움직이는 그들은 우리 사회의 …

Dragon Quest 11 is a popular role-playing game developed and published by Square Enix. One of the exciting features of …

Live Casino House Japan offers a thrilling and interactive online gambling experience for players in Japan. With a wide variety …

몇 번의 클릭으로 흥분과 아드레날린이 있는 온라인 스포츠 베팅의 세계에 오신 것을 환영합니다. 큰 성공을 거두고 좋아하는 팀을 지원할 수 …

Toto88 is an online platform that offers a wide range of sports betting options to its users. With a focus …

A training collar, also known as an electronic, remote, or shock collar, is a type of collar used to train …

Are you looking for an exciting and thrilling way to pass the time? Look no further than playing slots not …

In today’s world, having a reliable mobile broadband connection is more important than ever. As our lives become increasingly digital, …

Living in Dallas Flex Group Real Estate is becoming an increasingly popular option for people looking to relocate and find …

Aviator Predictor is a revolutionary tool that provides casino gamers with predictive analysis and data-driven insights. It helps players make …

From online banking to streaming services, the internet has become a necessary part of life. Despite the convenience, it brings, …

If you’re new to online betting on horse racing, the process may seem intimidating at first glance. But with the …
No matter if you need installation, repair, maintenance or replacement services, San Diego plumbers are available to get the job …

Your home’s garden is one of the first things visitors see when they come to your house. It can be …

Dogs come in all shapes and sizes, and there’s a perfect type of pup for every family out there. From …

The best gift for Christmas is anything but from the heart. One example could be a new car. A new …

There are so many delicious traditional foods in the Philippines! It’s hard to choose just a few, but here are …

As a casino player, it is important to understand how bonuses and promotions work. They can be a great way …

There are a lot of slot dana 5000 online casinos to choose from, so it can be hard to find …

Football shirts come in a variety of materials and styles. The breathable fabric can be made from a man-made polymer, …

Онлайн-казино Вавада предлагает более 4500 разнообразных игр. Каждый зарегистрированный клиент может выбрать любой слот или другой симулятор, поставить деньги и …

Starting a fire in a fireplace is relatively easy. There are a few key steps that are worth noting though …

Казино Vavada известно многим любителям азартных игр. Это заведение выбирают сотни тысяч игроков по всему миру, ведь это одно из …
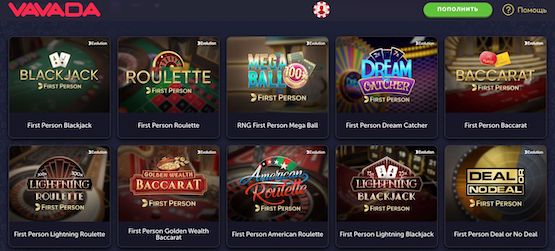
Погрузитесь в атмосферу азарта вместе с онлайн казино Vavada ! Отдохните от рабочих и семейных проблем и быта – регистрируйтесь в лучшем …

Если вы любите играть в казино, но не нашли достойную площадку, то советуем обратить свое внимание на игровой клуб Вавада. …
Getting motivated can be an ongoing process. Many people have a difficult time maintaining their motivation levels. This can be …
Having a properly maintained roof in Nashville is one of the most important aspects of owning a home. It will …

Whether you are a gambler, enjoy online games or you are new to the online world, you will find that …
If you’re looking for a luxury car rental service in San Diego, Ele-Fonts recommends elite black car services . The …
When you have problems with your water heater, it is important to look for the right professionals to take care …
Proper tile maintenance is critical to a pool. Tiles in a pool must be repaired as soon as they start …
Alcatraz Lock in Phoenix is a well-known company in the Phoenix metropolitan area that provides locksmith services to homes and …

If you are in need of a window cleaner in Arizona, here are some reasons why you should hire a …

If you have a flat roof on your property, it’s important to know the basic details of how a replacement …

If you are looking for a private driver in New York City, Ele-Fonts has the best recommendations for a luxury …

You may have heard about these special cats that many pet lovers are buying for pets. These unique cats are …

Healthy family picnic ideas on a budget don’t have to be complicated. You can make a variety of delicious foods …

The biggest private hire fleets in the UK are concentrated in the North-west and South-east outside London. The region has …

If you’ve decided to get a dog as a family pet, here are some things to keep in mind: Choosing …

Blackjack is one of the most popular games you can play in an online casino. This popular card game is …

Online casinos provide a number of benefits to users. While it used to be necessary to drive to Las Vegas …

Paris has a number of great places to visit with kids. The most popular being EuroDisney otherwise known as DisneyLand …

Here is some information to help you understand the product better. Read on to learn about Cannabinoids, Terpenes, and Chemical …

Slot machines are a popular form of entertainment for players, and you may have already played online slot games. These …
Humorous t-shirts are a great way to handle conflicts. They’re wacky, sarcastic, and very funny . They’re also a great …

If you’re planning a major house clearance, skip hire may be the best option for your needs. Skips are large, …

Traveling is the act of moving from one geographic location to another for various purposes, including leisure, business, education, or …

If you’re looking for the best winter travel destinations for Christmas 2022, you’ve come to the right place. These destinations …

If you’re looking for the best ski resorts in Europe, you’ve come to the right place. Here’s a look at …

Travel is the practice of moving from one geographical location to another. This can be done by automobiles, airplanes, boats, …

There are several different methods of hair transplant surgery. There is the traditional method, advancement flap surgery, follicular unit extraction, …

If you’d like garden ideas , Ele-Fonts has some simple yet effective ideas for you. These include growing plants in …

UK Football is one of the most popular sports in the world. Amateurism and Industrialization all played an important role …

Among the basic etiquette and golf tips you can follow is the proper posture while playing the game. To achieve …

If you’re looking for gifts for mums, you’ve come to the right place. We’ve rounded up some of the best …

If you need to change the locks in your home or office, you need to look for a good locksmith …

To sell your property, it is important to market it in the best way possible. One way to do this …

Commuter, BMX, and fixed-gear bikes are some of the various types of bicycles. These types of bicycles are easy to …

In the summer, there are plenty of activities for children to enjoy in Madrid. The city offers several parks, including …